Expressvpn Glossary
System security

What is system security?
System security is the protection of a computer system and its components (devices, operating systems, applications, and data) from threats that could compromise them. It aims to prevent unauthorized access, unauthorized changes, and disruptions that interfere with normal operation.
System security is commonly organized around three outcomes: confidentiality, integrity, and availability. These principles help ensure information remains confidential, accurate, and trustworthy, and available to authorized users when needed.
System security is not only technical. It depends on a combination of people, processes, and technology to reduce risk and keep systems operating reliably.
How does system security work?
System security works as an ongoing process rather than a single control. Key activities include:
- Asset identification and risk assessment: Systems, applications, devices, and data are identified and evaluated to determine which assets need protection and which threats are most relevant.
- Least privilege and segmentation: Access is limited to what is necessary for a role or system function. Sensitive components are separated to reduce the impact of a compromise.
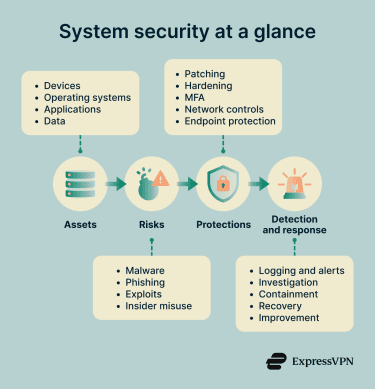
- Updates and secure configuration: Operating systems and software are kept up to date, and systems are configured securely to reduce exposure to known vulnerabilities.
- Monitoring and detection: Logs, alerts, and behavioral signals are analyzed to identify suspicious or abnormal activity, often using intrusion detection and prevention systems (IDPSs), endpoint monitoring, and centralized logging.
- Response, recovery, and improvement: Incidents are contained, and systems are restored. Controls are reviewed and strengthened to reduce the likelihood of similar events.
Types of system security
System security is implemented through multiple, overlapping layers, each designed to protect a different part of a computing environment.
| Type | What it covers |
| Physical controls | Protect hardware and infrastructure using locks, access badges, surveillance, and secured facilities to prevent unauthorized physical access. |
| Operating system hardening | Secures operating systems through configuration settings, service management, permission controls, and reduced attack surface. |
| Network security | Protects systems and data in transit using firewalls and intrusion detection or prevention systems to control and monitor traffic. |
| Endpoint security | Secures individual devices with antivirus software and endpoint detection and response agents to detect and stop malicious activity. |
| Identity security | Protects accounts, credentials, and authentication processes using multi-factor authentication (MFA), strong credential management, and identity lifecycle controls. |
Why is system security important?
System security is important because it reduces the likelihood of system compromise or misuse. Without appropriate safeguards, organizations and individuals can face operational disruption, financial loss, and reputational harm.
System security helps reduce the risk of malware, ransomware, and account takeover by reducing unauthorized access and the spread of malicious software. It also protects personal and business data by preventing unauthorized disclosure or alteration.
By helping prevent incidents and support faster containment and recovery, system security can reduce downtime and related costs. It also supports legal and compliance requirements mandating security controls and helps sustain trust in digital services that handle data and accounts.
Where is system security used?
System security applies to any computing system that stores, processes, or transmits information, including personal, organizational, and national-scale systems.
- Home devices: Smartphones, laptops, home routers, and connected devices use system security to protect personal data and limit unauthorized access.
- Businesses: Workstations, servers, internal networks, and software platforms use system security controls to protect organizational operations and assets.
- Critical infrastructure and industrial systems: Industrial control systems and operational technology environments use system security to protect essential services and industrial processes.
- Public sector and education networks: Government agencies and other large institutions apply system security to protect information and maintain reliable operations at scale.
- Cloud environments and virtual machines: Cloud environments apply system security through a shared responsibility model, while virtualized environments use controls to protect hosts, hypervisors, virtual networks, and workloads.
Risks and privacy concerns
System security risks and privacy concerns often result from gaps in configuration, maintenance, or oversight. Misconfigurations can expose services or data through overly permissive settings, while outdated software can leave known vulnerabilities unpatched and available for exploitation. Password reuse can also enable credential stuffing, increasing the risk of account compromise through automated reuse of stolen credentials.
Privacy risks can also arise from how security is operated. Excessive telemetry collected by monitoring and diagnostic systems can capture behavioral or usage data, creating privacy concerns when collection and retention are not properly governed. Security tools can also collect sensitive logs, and these detailed activity records may include confidential or regulated information if they are not appropriately protected.
Further reading
- How can you protect your home computer?
- Attack surface reduction explained: Principles, techniques, and tools
- VPNs, firewalls, endpoint security: What does your team really need?
- 2FA vs. MFA: Key differences and how to choose the right one
- Malware vs. virus: Key differences explained

