Expressvpn Glossary
Forward proxy

What is a forward proxy?
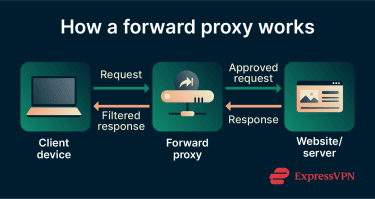
A forward proxy is a server that acts as a controlled gateway between users or devices and the public internet. Instead of connecting directly to external websites or services, client requests first pass through the proxy server, which forwards them on the client’s behalf.
How does a forward proxy work?
A forward proxy typically follows these steps:
- A client sends a request to access a website or online resource.
- The request is directed to the forward proxy server instead of the destination.
- The proxy evaluates the request and applies authentication, filtering, or policy rules.
- The proxy forwards the request to the destination server.
- The destination server responds to the proxy.
- The proxy relays the response back to the client.
Types of forward proxy
Forward proxies can be categorized based on protocol:
- HTTP proxy: Handles standard unencrypted web traffic; commonly used for basic web filtering and access control, but doesn’t protect data in transit.
- HTTPS proxy: Handles encrypted HTTPS traffic; depending on configuration, it may simply relay encrypted traffic or perform Secure Sockets Layer (SSL) / Transport Layer Security (TLS) inspection to decrypt, inspect, and re-encrypt traffic.
- SOCKS proxy: Operates at a lower level and supports both Transmission Control Protocol (TCP) and User Datagram Protocol (UDP) traffic, allowing it to handle a wider range of applications beyond just web traffic.
Proxies can also be classified by deployment and usage model:
- Transparent proxy: Intercepts traffic without requiring client-side configuration; often used in corporate networks or schools to enforce policies and monitor usage.
- Residential or rotating proxy: Uses multiple IP addresses to distribute requests across different network identities; commonly used for web scraping and automation.
Why is a forward proxy important?
Forward proxies can give organizations centralized control over outbound traffic. They can use them to apply access rules, filter content, monitor usage, and enforce security policies from a single point. Forward proxies also make it easier to log and audit network activity because all outgoing requests flow through the proxy.
From a security perspective, forward proxies help to isolate internal systems from external servers. Outside destinations communicate with the proxy rather than directly with individual devices, which reduces exposure. Proxies can also provide a layer of privacy, since destination servers see the proxy’s address instead of the originating client’s internal IP address.
Where are forward proxies used?
Forward proxies are used in environments where outbound internet access requires control, monitoring, or policy enforcement, including:
- Corporate networks that regulate employee internet access.
- Schools and public networks that filter or restrict content.
- Secure web gateways, which often operate as forward proxies to inspect outbound traffic.
- Research and automation environments that route requests through shared network infrastructure.
- Systems that require centralized logging of network activity.
Risks and privacy concerns
Using a proxy server can introduce various privacy and security risks:
- Proxy operator visibility: Operators can monitor browsing activity, including visited websites and connection metadata. For encrypted traffic (HTTPS), the proxy may see only metadata unless configured for SSL/TLS inspection.
- Credential or data exposure: Misconfigurations can leak login credentials, tokens, or sensitive data.
- Online activity stored in logs: Proxy logs often record requests and user identifiers, which may create persistent records of behavior.
- Malicious free proxies: Untrusted or public proxy services may sell or manipulate user data.
Further reading
- What is a web proxy, and how does it work?
- SOCKS proxy explained: What is it and how it works
- What is a reverse proxy? Secure guide for VPN users
- What is an open proxy, and why should you be cautious?
- What are anonymous proxies, and how do they work?
- Top 12 VPN myths debunked
- What is computer networking and how VPNs fit in


