Online gaming security: How to stay safe from hacks, scams, and toxic players
Gaming is about more than just playing games. These days, players also chat, use voice calls, share content, and make trades. All this can happen in-game and on third-party platforms. While this adds a new social dimension to multiplayer gaming, it can also increase the risk of privacy loss, harassment, scams, and other harms.
This guide explores the online gaming security landscape. It looks at common threats, the measures developers take to improve safety, and the steps gamers can take to protect themselves.
Current state of online gaming security
The gaming industry is constantly expanding and changing, so new threats continue to emerge. The risks a gamer faces depend on the games they play, the services they use, their personal security habits, and their broader online behavior. That said, many scams and risks are widespread enough that it’s worth understanding the general threat landscape.
How secure is online gaming today?
Gamers can significantly reduce their risk, but online play still comes with inherent security and privacy challenges. Multiplayer gaming typically involves creating an account, sharing some data with a platform or service, and connecting to remote servers. Like other digital services, games and gaming platforms can also be affected by data breaches, account compromise, malware, and other cyberattacks.
Large global communities, real-money purchases, and in-game economies can create opportunities for scammers, harassers, and other bad actors. Moderating all of this consistently is difficult, especially when activity extends beyond the game itself to third-party chat apps, marketplaces, boosting services, and other communities. These services may be useful, but they can also expose gamers to phishing, fraud, unwanted contact, and malicious downloads.
Why gamers are targeted
There are several reasons bad actors target gamers. Common motives include financial gain, attention, and a desire to harass or disrupt others. Threats can come from other players, organized scammers, and broader cybercriminal groups.
Gamers often spend a lot of time online, regularly interact with strangers, and may buy digital items or services. Some gaming spaces also include children and teens, who may be more vulnerable to manipulation, grooming, or scams.
The online gaming ecosystem also offers opportunities for abuse beyond gameplay. Compromised accounts can be used for spam or fraud, valuable in-game items and currencies can be stolen, and security flaws in game clients, servers, mods, or related services have at times enabled serious attacks, including malware delivery or remote code execution.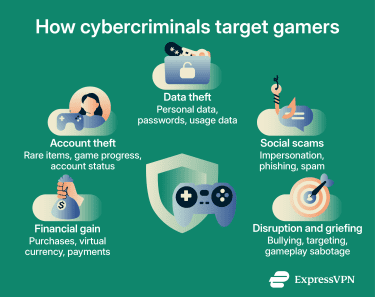
Understanding online gaming security
There are many different factors that affect online gaming security. Game developers and infrastructure operators play a significant role, but player behavior is also important, especially for scams that rely on social engineering.
What is online gaming security?
Online gaming security can be broken down into different categories. Under each category, the primary security responsibility may lie with the game or platform owners, the players, or both.
These are typically the main areas of concern:
- Protecting gaming accounts: User accounts need protection against unauthorized access. This includes good password practices, two-factor authentication (2FA), and, in some cases, additional verification or age checks required for certain features or jurisdictions. Game developers should provide secure access and verification methods, but gamers must use them effectively.
- Safeguarding player data: Customer data must be securely collected, transmitted, and stored to reduce the risk of data breaches and leaks. Players are responsible for being selective about what information they share and how they communicate with other users. Developers, in turn, are responsible for protecting this data from exposure.
- Preventing abuse, cheats, and scams: Developers should help protect players from dangerous and rule-breaking behavior through reporting tools and automated systems. These should target cheaters, scammers, spammers, and other abusive behavior. Players should use these systems and follow the codes of conduct.
- Securing gaming platforms and infrastructure: Developers and infrastructure teams should implement countermeasures to reduce the risk and impact of attacks that disrupt normal game operations or players’ ability to access them. This may involve mitigating distributed denial-of-service (DDoS) attacks and fixing serious exploits that affect servers, clients, accounts, or gameplay integrity.
Security standards and frameworks in gaming
There aren’t many widely cited or universally followed security frameworks specifically for video games. Instead, game developers, publishers, and related services tend to rely on broader cybersecurity standards and assurance frameworks.
For example, the International Organization for Standardization (ISO) / International Electrotechnical Commission (IEC) 27001 is a leading standard for information security management systems (ISMS). Some companies in the industry are certified to ISO/IEC 27001, though this generally applies to organizational security management and infrastructure rather than game design itself.
Other commonly referenced frameworks and assurance models include the National Institute of Standards and Technology (NIST) Cybersecurity Framework and System and Organization Controls 2 (SOC 2) reporting. When it comes to data protection, platforms may also need to comply with laws such as the General Data Protection Regulation (GDPR) and the Children's Online Privacy Protection Act (COPPA), depending on where they operate, whom they serve, and what data they collect.
These standards and laws aren’t tailored specifically to online gaming, but they can still help organizations protect user data, implement security controls, and manage cybersecurity risks.
The role of gaming companies
Game developers, publishers, and companies hosting server infrastructure all play a role in maintaining security. Their responsibilities often overlap, but each may contribute to the following safety measures:
- Data protection: Encrypting sensitive user data helps reduce the risk of exposure or theft. Organizations commonly use protocols such as Transport Layer Security (TLS) for data in transit and may also encrypt sensitive data at rest, though exact implementations vary.
- Secure authentication: Offering 2FA helps protect user accounts by making unauthorized access more difficult. Developers allow gamers to combine passwords with additional factors, such as one-time passwords (OTPs) and authenticator apps.
- Network protection: Firewalls and intrusion detection systems (IDSs) may help block or detect attacks before they affect game systems. Developers may also use additional protections to reduce the impact of DDoS attacks or unauthorized access to servers.
- Anti-cheat systems: Games and gaming services often use automated anti-cheat systems to identify cheating. Some of these tools require a high level of access to the gamer’s device, especially on PC, so operators need to be transparent about how they work and how player data is handled.
- Fraud prevention: Fraud detection systems automatically monitor accounts and game servers for suspicious activity. Depending on the behavior, it may trigger an automated restriction or be escalated for investigation. Suspicious activity may include repeated failed login attempts, unusual sign-in patterns, or sudden location changes.
- Internal security audits and testing: Regular security audits may help catch vulnerabilities or control gaps before they're exploited. They also help gaming companies assess their practices for user data protection, authentication, incident response, and related areas.
- Age restrictions: Platforms and games may implement safeguards to help prevent underage users from accessing content or features intended for adults. Depending on the jurisdiction or feature, this can include age gates, parental controls, or identity and age checks.
- Reporting and moderation: Games and platforms usually provide reporting systems and human moderation to address issues that automated tools may miss, such as harassment or bullying. At the same time, they should have safeguards to reduce abuse of reporting systems and unfair penalties.

Identifying common online gaming risks
While games, gaming platforms, and gaming infrastructure have various security measures in place, none can guarantee protection against every threat. Players also need to understand common security risks to reduce the chance of falling victim to cybercriminals.
Account takeovers and credential stuffing
For many cybercriminals, the first goal is to gain access to a target's account in order to use it for their own purposes. Attackers can obtain credentials through social engineering, data breaches, malware, or brute force attacks.
Credential stuffing is when attackers use stolen username-password combinations from one breach to attempt logins on other accounts. This works because many people reuse the same login details across multiple services.
Once attackers gain access to an account, they may change the password immediately, making recovery more difficult. From there, they may make unauthorized purchases, transfer valuable items, or steal funds.
Phishing and fake giveaways
Phishing is another common way cybercriminals take over accounts. Usually, it involves directing the target to a fake login page in the hope that they’ll give away their password.
For example, scammers may impersonate gamemasters or customer support, claim there’s an issue with your account, and provide a link that supposedly resolves it.
Attackers often carry out phishing via email, social platforms, or chat tools. They may lure victims by promising freebies, such as in-game cosmetics, limited-edition items, or free downloadable content (DLC). Promises of free giveaways aren’t always tied to phishing. These offers aren't always phishing, but they should be treated with caution because they may also be linked to other scams or malware.
Malware, cheats, and Trojan mods
Cybercriminals use various types of malware to infect player systems. They may disguise malware in free (or cheap) game files, DLC, mods, or cheating tools to trick players into downloading and installing it.
Such threats are often spread through chat platforms, gaming communities, forums, and third-party download sites, including Discord. Some scam messages also promise free Nitro or similar rewards. Depending on the lure, the victim may encounter phishing, malicious downloads, token theft, or other forms of account compromise. Discord warns that official Discord messages will never ask for a password or account token.
Ransomware, spyware, and keyloggers can also be spread through malicious links, downloads, or files shared across gaming communities and other third-party platforms.
DDoS attacks and match disruptions
DDoS attacks aimed at gamers bombard hosting servers with traffic. This can disrupt gameplay by causing lag, disconnects, or outages.
Some games rely on player-hosted servers to facilitate online play. These can also be targeted by DDoS attacks, sometimes due to rivalries or attempts to disrupt play.
It’s also possible for attackers to target an individual player if they can discover the player’s IP address or otherwise reach the player’s internet connection directly. Public figures like streamers are more visible targets, but the risk is not limited to them.
In-game scams and trading fraud
Another common scam is to offer to trade players rare in-game items for real-world money, virtual currency, or other digital goods. Once the victim completes their part of the deal, the scammer may disappear or deliver something less valuable. Alternatively, the scammer may try to reverse the transaction through chargebacks or by abusing customer-support processes, while keeping what they received.
To enable the scam, attackers often convince players to complete part of the trade outside approved in-game systems. These scams are commonly initiated through third-party websites, Discord servers, or forums, where enforcement may be weaker or less visible.
It’s also worth noting that many online games restrict or prohibit real-money trading outside approved systems, though the exact rules vary by game and platform. Violating those rules can lead to account penalties even when no scam occurs. For example, Steam doesn't allow money such as PayPal, gift cards, or wallet credit to be added to trade offers outside its approved systems.
Chat and privacy risks
One of the most common privacy risks in online gaming comes from oversharing personal information. Sharing sensitive details with others can increase the risk of cyberstalking, abuse, account compromise, and phishing.
AI voice deepfakes can add another layer of risk in voice-chat environments. Voice cloning may be used for impersonation, social engineering, or abuse. The Federal Trade Commission (FTC) has issued a broader warning about voice-cloning scams.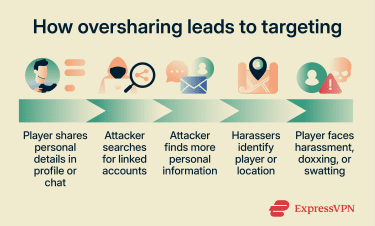
In-game harassment
In addition to verbal abuse, players may face griefing and other forms of targeted harassment. Griefing is deliberate in-game behavior meant to disrupt, frustrate, or spoil another player’s experience. One common form is when a larger group of players gangs up on a smaller group or individual to stop them from playing normally.
Stream sniping is when players use a streamer’s live feed to target them in-game. Other behaviors, such as dogpiling, brigading, or ganking, can also be used to harass players, though the exact meaning and severity may depend on context and the game.
Many games have anti-bullying policies, but they're often difficult to enforce. Moderators may lack full context, and some reports may not clearly distinguish harassment from ordinary competitive play.
Such harassment is not just an inconvenience. It can create real safety and privacy risks, especially when it escalates into stalking, threats, doxxing, or swatting.
Best practices for secure gaming
You can take proactive precautions to protect your privacy, account integrity, and overall gaming experience. Most of these tips apply across all online games and platforms.
Protecting personal information
On games or any other online platform, it’s advisable that you don't share sensitive or personal information with strangers. Another common mistake is sending potentially sensitive messages to friends via public or team channels.
It’s advisable to be careful even with those you consider friends. They may have bad intentions, fall out with you later, or have their account compromised.
As a rule, the best way to stay safe is to separate your online accounts from your real-world identity. This means avoiding personal details in a gamertag or public profile. The same advice applies to community and communication channels, whether in-game, on forums, on Discord, or on other platforms
Setting up accounts securely
As an extra precaution, you may want to use a separate email account for gaming and avoid linking it to other third-party services unnecessarily. This can help limit the impact if a gaming account is exposed. At a minimum, it may be wise to avoid using an email address that contains personal information.
Also, check the game or platform’s privacy and sharing settings. In many cases, you can choose what information is shared publicly, with friends only, or hidden entirely. Some platforms also offer family or parental controls for underage users.
Finally, secure account-recovery options can help restore access if an account is compromised or login details are forgotten.
Avoiding password reuse and weak passwords
Creating long, unique passwords makes it harder for attackers to access your account using password-guessing attacks. To reduce the risk of credential stuffing, don’t reuse passwords from other accounts. Password managers can also help generate and store strong, distinct passwords.
Using two-factor authentication
Wherever available, set up 2FA to help protect your accounts from unauthorized access. Many major gaming platforms support 2FA or similar account security tools, such as OTPs or dedicated authenticator apps. Steam, for example, offers Steam Guard as an additional layer of security.
Enabling login alerts can help flag suspicious access. It's also a good idea to review active sessions or authorized devices and remove any that are not recognized. This can force reauthentication and help limit unauthorized access.
Spotting scams and social engineering
Be mindful of scams both inside and outside of game environments. Scams may begin on platforms such as Steam or Discord just as easily as in games themselves. Avoid making trades outside games or approved systems. Pressure, urgency, or unusually generous offers can all be warning signs.
Be especially cautious with unexpected offers that seem too good to be true. Private messages offering free digital goods should be treated with suspicion unless verified through official channels. Some games and platforms publish clear guidance on what official messages look like.
Be wary of unusual messages from friends. When attackers compromise a Discord or Steam account, they often message that person's contacts to spread scams or malicious links. If a message seems off, verify it through another channel or ask questions only the real person would be likely to answer.
As a rule, confirm giveaways, account issues, and special events via official websites or in in-app notices rather than through links in messages.
Securing your device
Security software can help detect some known malware and malicious files, but it doesn't stop every threat you may face. This can still be useful against threats delivered through email attachments, downloads, or malicious files shared through gaming communities.
Consoles generally don't use traditional antivirus tools as PCs do, but many console gamers still use computers or phones alongside their gaming accounts and communities, so device protection still matters.
It is also worth noting that some mods may trigger false positives in security tools. For that reason, be cautious with mods and other files. Avoid files sent via private messages or on unrelated forums, and prefer well-known distribution sites with a visible review history.
Keeping your games, gaming platforms, drivers, operating system, and software up to date is essential. The Cybersecurity and Infrastructure Security Agency (CISA) notes that patches and updates address security vulnerabilities, and regularly installing them helps protect devices and applications.
Securing your network
Using a virtual private network (VPN) encrypts traffic between the device and the VPN service and helps mask your device’s public IP address from other users. In some situations, this may reduce direct exposure to certain attacks. If DDoS targeting is a concern, a VPN can be one helpful protective measure, but it's not a guarantee. Xbox support lists using a VPN as one option for reducing exposure to DoS attacks.
Many commercial VPNs offer apps for Windows, Mac, iOS, and Android. Installing the app can protect traffic from apps and games on that device. A router-level VPN can extend similar protection to devices connected through that router, depending on the setup.
Gaming consoles generally don't support native VPN apps the way PCs and phones do. Some VPN services, including ExpressVPN, offer smart DNS or router-based workarounds, but these vary by provider and don't provide the same protection as a full VPN tunnel
Using secure payment methods
Reputable gaming platforms typically support payment methods such as credit cards, PayPal, and digital wallets. One of the most important protections is securing the platform account itself to prevent the abuse of saved payment methods.
When using third-party sites, check whether they have a trustworthy reputation and a clear payment and dispute process. At a minimum, the site should use Secure Sockets Layer (SSL), and any entity handling card data should follow the Payment Card Industry Data Security Standard (PCI DSS) requirements where applicable.
Using payment methods that support dispute or chargeback options may increase the chances of recovering funds after a scam, but recovery is not guaranteed.
What to do if your gaming account gets hacked
The key to limiting the damage is to act quickly. If you catch an account breach early enough, you may be able to secure the account yourself. However, you may need the help of customer support if the hackers were able to completely lock you out.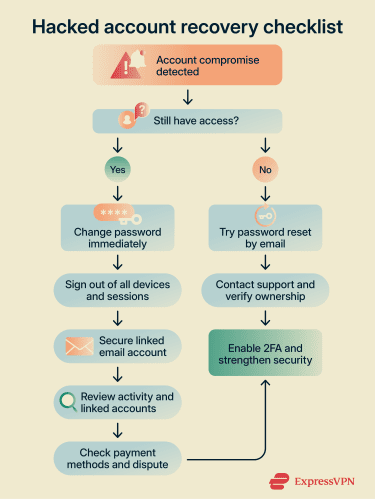
Immediate actions to take
Assuming you still have access to your account, immediately perform the following steps:
- Change password: Create a new, unique, and strong password. This may log out other devices and apps, but some platforms require a separate step to sign out all sessions, so check the account security settings as well.
- Adjust 2FA settings: If you have reason to believe your 2FA method has been compromised (for example, if your phone was stolen or your email was hacked), change it to a different secure method. If you lose access to your 2FA method, you may need backup codes or to contact customer support to recover your account.
- Log out of sessions/devices: Check for any apps or devices that seem unfamiliar. Revoke unrecognized logins and end active sessions to force devices to sign in again with the new credentials.
- Check the linked email: Make sure the email associated with your gaming account was not compromised as well. If it was, change that password too, sign out of other sessions, and review recovery and forwarding settings.
- Review activity: Check your chat history, purchase history, and gaming activity. You may need evidence to request a refund or to explain the actions the attacker took that violated platform rules.
- Secure payment details: Contact your card issuer, bank, or wallet provider right away about unauthorized charges, and use any card-lock or account-protection features they offer. Consider replacing payment cards if you have reason to believe the details were exposed.
How to recover your account
A hacker may change your email, password, or other security settings so that you’re unable to access your own account. If you enter the correct credentials and still can’t get in, that may be what happened, though other account-recovery issues are also possible.
If the account is still tied to the original email, you may be able to recover it yourself through a password reset or other self-service recovery steps. You should also check your email and any other accounts that use the same password to ensure they’re not compromised too.
If both the email and password have changed, you’ll likely need to contact customer support for the relevant gaming platform. In many cases, support will ask for proof of ownership, which may include details such as purchase history, previous account information, or other identifying information tied to the account.
After recovering your account, make sure to check for any suspicious activity. If the platform doesn't require it automatically, set a new strong password and sign out of other devices or active sessions where possible
How to prevent it from happening again
The first step is to understand how the breach may have happened. Knowing the likely cause can help reduce the chance of repeating the same mistake. Checking breach alert sites like Have I Been Pwned may show whether your email address appeared in a known data breach, which can help indicate whether exposed credentials played a role.
To take it a step further, consider using an identity monitoring service. For example, ExpressVPN customers in the U.S. on eligible Advanced and Pro plans can access Identity Defender features such as breach alerts and credit monitoring.
If you don’t recall a specific phishing attempt or downloading a suspicious file, you may not be able to immediately discern how the account was compromised. Reviewing linked accounts, email addresses, and login activity may still help identify the likely cause.
To reduce the risk of breaches, enabling 2FA is one of the easiest and most effective steps. Where available, stronger phishing-resistant authentication methods provide even better protection.
How to choose secure gaming platforms
It can be difficult to know exactly how secure an online game or platform is. However, reviewing its documentation, support center, and community feedback can reveal a lot about its security features and practices.
Companies often don’t disclose every technical detail about their security measures, but there are still several things you can look into. These include:
- Reliable reputation: Prefer widely used publishing and distribution platforms, games from established developers, and officially supported third-party services.
- Strong account security: Look for platforms that support 2FA, login alerts, session management, activity history, and other account-security features.
- Uses modern authentication standards: Where relevant, review whether the platform supports modern identity and authorization standards such as Open Authorization (OAuth) 2.0 and OpenID Connect (OIDC). OpenID Connect is the identity layer built on top of OAuth 2.0.
- Data protection compliance: Check whether the company explains which privacy laws it complies with, such as the GDPR, where applicable, and whether it reports certifications or alignment with standards such as ISO/IEC 27001.
- Transparent policies: Review privacy and data-sharing policies for unclear, overly broad, or problematic practices.
- Active moderation: Look for clear reporting systems, published enforcement rules, and signs that abuse reports are actively handled.
- Regular security updates: Check whether the game or platform appears to be actively maintained and whether developers issue updates that address bugs, account security, and other security issues.
- Safe payment processing: Check whether the platform offers payment methods you trust and includes fraud protection or dispute support processes.
- Privacy and sharing settings: Make sure the game or platform lets you adjust privacy and sharing settings to fit your preferences.
- Accessible support: Check for dedicated support channels, account recovery documentation, and clear help for security-related issues.
FAQ: Common questions about online gaming security
What are the risks of online gaming?
What is online gaming security?
How can I stay safe while online gaming?
What are the most secure gaming platforms?
How can I protect my gaming account from being hacked?
What is two-factor authentication (2FA), and why is it important for gaming?
How do I spot phishing scams in games and Discord?
Is it safe to buy skins or trade items online?
Take the first step to protect yourself online. Try ExpressVPN risk-free.
Get ExpressVPN